Changing the current user causes active camera clients in apps owned by the previous user account to be evicted. Access to the camera is limited to user profiles owned by the current device user. In practice, this means that a “Guest” account, for example, will not be able to leave running processes that use the camera subsystem when the user has switched to a different account.
Runtime
The ART runtime now properly implements access rules for the newInstance() method. This change fixes a problem where Dalvik was checking access rules incorrectly in previous versions. If your app uses the newInstance() method and you want to override access checks, call the setAccessible() method with the input parameter set to true. If your app uses the v7 appcompat library or the v7 recyclerview library, you must update your app to use to the latest versions of these libraries. Otherwise, make sure that any custom classes referenced from XML are updated so that their classconstructors are accessible.
This release updates the behavior of the dynamic linker. The dynamic linker now understands the difference between a library’s soname and its path ( public bug 6670), and search by soname is now implemented. Apps which previously worked that have bad DT_NEEDED entries (usually absolute paths on the build machine’s file system) may fail when loaded.
The dlopen(3) RTLD_LOCAL flag is now correctly implemented. Note that RTLD_LOCAL is the default, so calls todlopen(3) that didn’t explicitly use RTLD_LOCAL will be affected (unless your app explicitly used RTLD_GLOBAL). WithRTLD_LOCAL, symbols will not be made available to libraries loaded by later calls to dlopen(3) (as opposed to being referenced by DT_NEEDED entries).
On previous versions of Android, if your app requested the system to load a shared library with text relocations, the system displayed a warning but still allowed the library to be loaded. Beginning in this release, the system rejects this library if your app's target SDK version is 23 or higher. To help you detect if a library failed to load, your app should log the dlopen(3)failure, and include the problem description text that the dlerror(3) call returns. To learn more about handling text relocations, see this guide.
APK Validation
The platform now performs stricter validation of APKs. An APK is considered corrupt if a file is declared in the manifest but not present in the APK itself. An APK must be re-signed if any of the contents are removed.
USB Connection
Device connections through the USB port are now set to charge-only mode by default. To access the device and its content over a USB connection, users must explicitly grant permission for such interactions. If your app supports user interactions with the device over a USB port, take into consideration that the interaction must be explicitly enabled.
Android for Work Changes
This release includes the following behavior changes for Android for Work:
- Work contacts in personal contexts. The Google Dialer Call Log now displays work contacts when the user views past calls. Setting
setCrossProfileCallerIdDisabled() to true hides the work profile contacts in the Google Dialer Call Log. Work contacts can be displayed along with personal contacts to devices over Bluetooth only if you setsetBluetoothContactSharingDisabled() to false. By default, it is set to true.
- Wi-Fi configuration removal: Wi-Fi configurations added by a Profile Owner (for example, through calls to the
addNetwork() method) are now removed if that work profile is deleted.
- Wi-Fi configuration lockdown: Any Wi-Fi configuration created by an active Device Owner can no longer be modified or deleted by the user if
WIFI_DEVICE_OWNER_CONFIGS_LOCKDOWN is non-zero. The user can still create and modify their own Wi-Fi configurations. Active Device Owners have the privilege of editing or removing any Wi-Fi configurations, including those not created by them.
- Download Work Policy Controller via Google account addition: When a Google account that requires management via a Work Policy Controller (WPC) app is added to a device outside of a managed context, the add account flow now prompts the user to install the appropriate WPC. This behavior also applies to accounts added via Settings > Accountsand in the initial device setup wizard.
- Changes to specific
DevicePolicyManager API behaviors:
- Calling the
setCameraDisabled() method affects the camera for the calling user only; calling it from the managed profile doesn’t affect camera apps running on the primary user.
- In addition, the
setKeyguardDisabledFeatures() method is now available for Profile Owners, as well as to Device Owners.
- A Profile Owner can set these keyguard restrictions:
KEYGUARD_DISABLE_TRUST_AGENTS and KEYGUARD_DISABLE_FINGERPRINT, which affect the keyguard settings for the profile’s parent user.KEYGUARD_DISABLE_UNREDACTED_NOTIFICATIONS, which only affects notifications generated by applications in the managed profile.- The
createAndInitializeUser() and createUser() methods have been deprecated.
- The
setScreenCaptureDisabled() method now also blocks the assist structure when an app of the given user is in the foreground.
EXTRA_PROVISIONING_DEVICE_ADMIN_PACKAGE_CHECKSUM now defaults to SHA-256. SHA-1 is still supported for backwards compatibility but will be removed in future. EXTRA_PROVISIONING_DEVICE_ADMIN_SIGNATURE_CHECKSUMnow only accepts SHA-256.- Device initializer APIs which existed in the Android 6.0 (API level 23) are now removed.
EXTRA_PROVISIONING_RESET_PROTECTION_PARAMETERS is removed so NFC bump provisioning cannot programmatically unlock a factory reset protected device.- You can now use the
EXTRA_PROVISIONING_ADMIN_EXTRAS_BUNDLE extra to pass data to the device owner app during NFC provisioning of the managed device.
- Android for Work APIs are optimized for M runtime permissions, including Work profiles, assist layer, and others. New
DevicePolicyManager permission APIs don't affect pre-M apps.
- When users back out of the synchronous part of the setup flow initiated through an
ACTION_PROVISION_MANAGED_PROFILE or ACTION_PROVISION_MANAGED_DEVICE intent, the system now returns aRESULT_CANCELED result code.
- Changes to other APIs:
- Data Usage: The
android.app.usage.NetworkUsageStats class has been renamed NetworkStats.
- Changes to global settings:
- These settings can no longer be set via
setGlobalSettings():
BLUETOOTH_ONDEVELOPMENT_SETTINGS_ENABLEDMODE_RINGERNETWORK_PREFERENCEWIFI_ON- These global settings can now be set via
setGlobalSettings():
WIFI_DEVICE_OWNER_CONFIGS_LOCKDOWN
 Android中View的滑動沖突——Android開發藝術探索筆記
Android中View的滑動沖突——Android開發藝術探索筆記
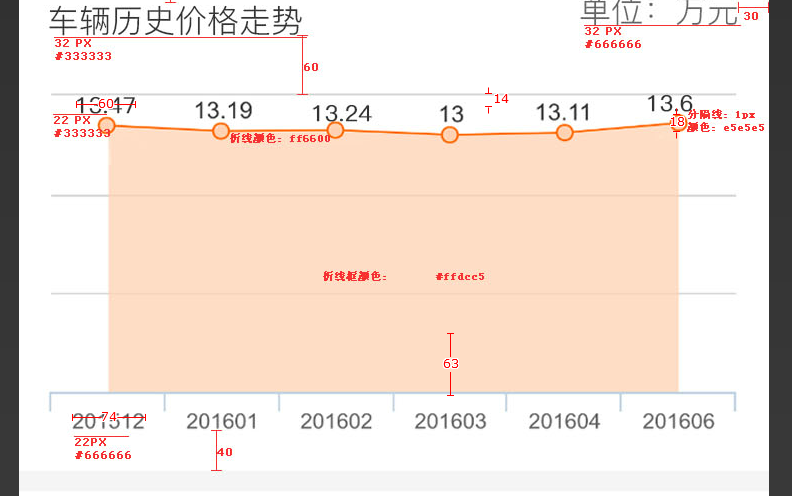 andoid 自定義view 畫折線圖,andoid折線
andoid 自定義view 畫折線圖,andoid折線
 [Android]Activity的生命周期
[Android]Activity的生命周期
 Android新手入門2016(16)--畫圖
Android新手入門2016(16)--畫圖